
There are two essential applications in the world of 2FA security: Authy (Twilio) and Google Authenticator which has some shortcomings (no backups, favored by Android at the expense of iOS).
We will see in this article how to set up an account on the Authy application and renew your 2FA on the concerned services.
Definition
Two-factor authentication (2FA) is a strong authentication method by which a user can access a computer resource (a computer, a smartphone or a website) after having presented two distinct proofs of identity to an authentication mechanism.
In cryptocurrencies, you may be asked for a 2FA code after your password.
It is strongly recommended that you enable the 2FA option in your user account settings to secure it.
This code is generated every 30 seconds. It comes from the link between the 2FA manager like Authy and the backup 2FA (private key) generated the first time by the dedicated service (Binance, Kucoin, Kryll) then linked to Authy.
In simplifying, it is like when you buy online by credit card and you receive the ephemeral visa verification code by sms or via your banking service application. In our case, you have a 2FA pass wallet application to several exchange services, emails or using the previous example, you find your ephemeral visa verification "pass" for each of your banks directly in the Authy application.
Example of Binance
When you enable the 2FA access feature, it is services like Binance that generate the secret private key for this "pass".
Whoever has this key can import this 2FA pass (Binance) in his Authy manager. When connecting after the password, the exchange will ask me for the ephemeral code of the "2FA Binance pass" that I will find by selecting my 2FA Binance pass already integrated in my Authy application.
The weaknesses of google Auth
- No automatic backup service for your services connected to the 2FA.
- You have to manage yourself the backup of the 2FA private key generated at the beginning when linking to a service.
- In case the phone is not repairable (in 11% of the cases) or stolen, you can't access to the Google Auth application and consequently the access to all your 2FA related services will be inaccessible unless you have saved your 2FA private keys when activating the 2FA link to the dedicated service.
- Proprietary format, impossible to export automatically to another 2FA manager (like Authy).
In its defense, no request for phone numbers and email during registration. It can also export 2FA connected services to a new phone with Google Auth but the old phone must be functional...
Why choose Authy (Twilio)
It offers an automatic backup of your 2FA connected services with the option "backup" on a secured cloud.
Without this option, you can still recover the access to your 2FA connected services within 24 hours after verification of your phone number provided during registration.
Secure connection to the application with the face id or the pine code unlike google Auth which only activates this security during the proprietary export.
Configure Authy
Compatible with Android and IOS you can download them via the following links:


The configuration is easy, you just have to enter an email and a phone number and then follow the standard procedure of linking 2FA to the concerned services (Binance, Kucoin, Kryll.io...).
Later in this article, we will review together these main steps of 2FA security between a customer’s account that will generate a 2FA backup with links by the user to the 2FA management service like Authy.
The final process will give the possibility to the user to copy his ephemeral 2FA code from the Authy application and to paste it during the connection (after password) to the customer account previously configured by the 2FA.
Renewal of your 2FA
If you want to change your 2FA management service from Google Auth to Authy. We will see how to renew your 2FA step by step by taking as an example the Kryll service. It will be the same methodology for Binance and Kucoin by going to revoke(or to delete) the 2FA in the settings of his account.
Example for Kryll.io
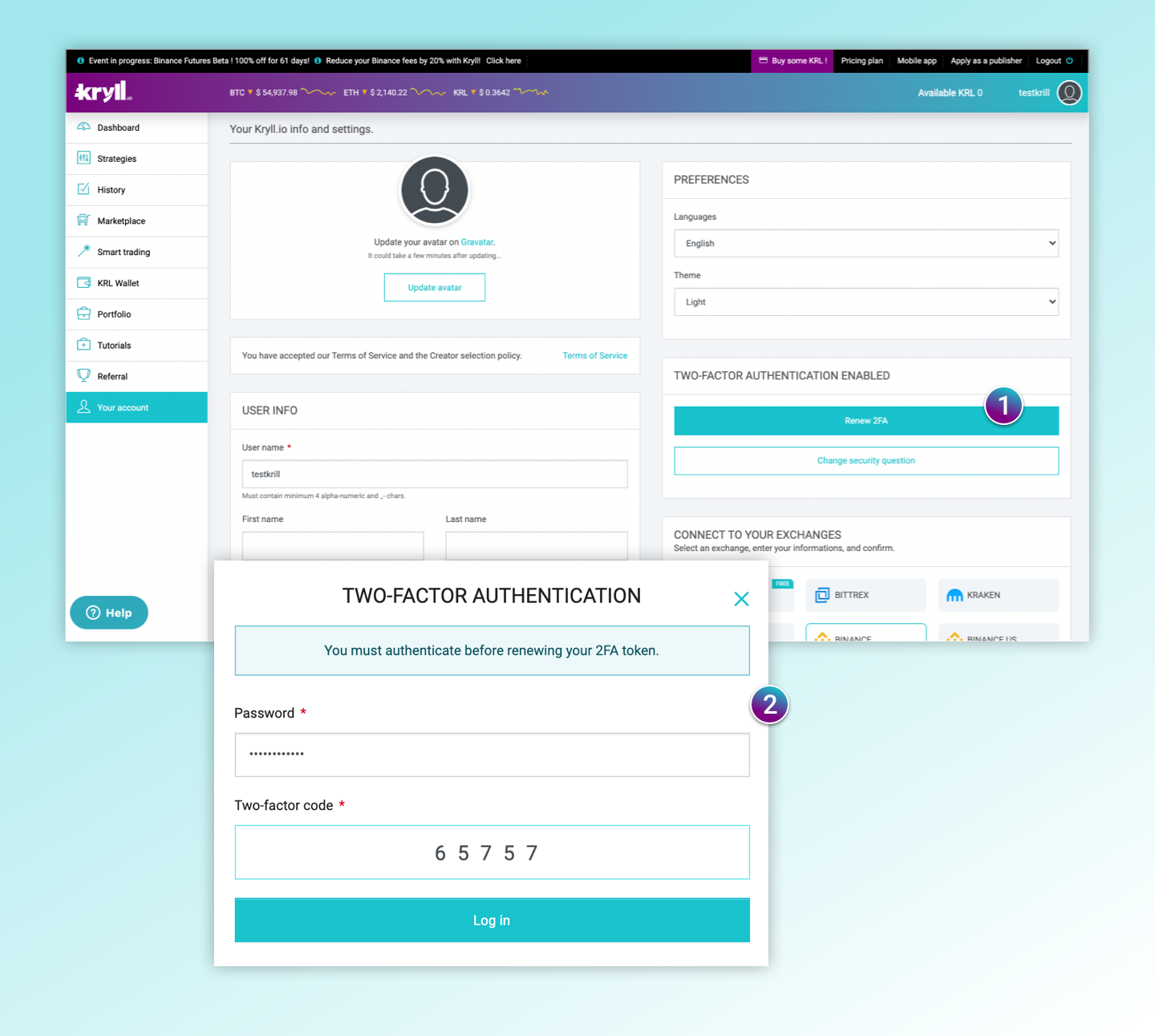
Step 1
Select renew 2FA in your Kryll account.
Step 2
A window opens and asks you to confirm the renewal of the concerned 2FA management service (here Google Auth).
Go to the Google Auth application to (some services ask to destroy the 2FA before creating another one), copy ephemeral code and paste in the 2FA renewal process.
A new window opens and a new backup 2FA is generated.All that's left to do is to secure it and/or link it to the Authy 2FA manager who will secure it in its cloud via the "backup" option.
Let's review these linking steps
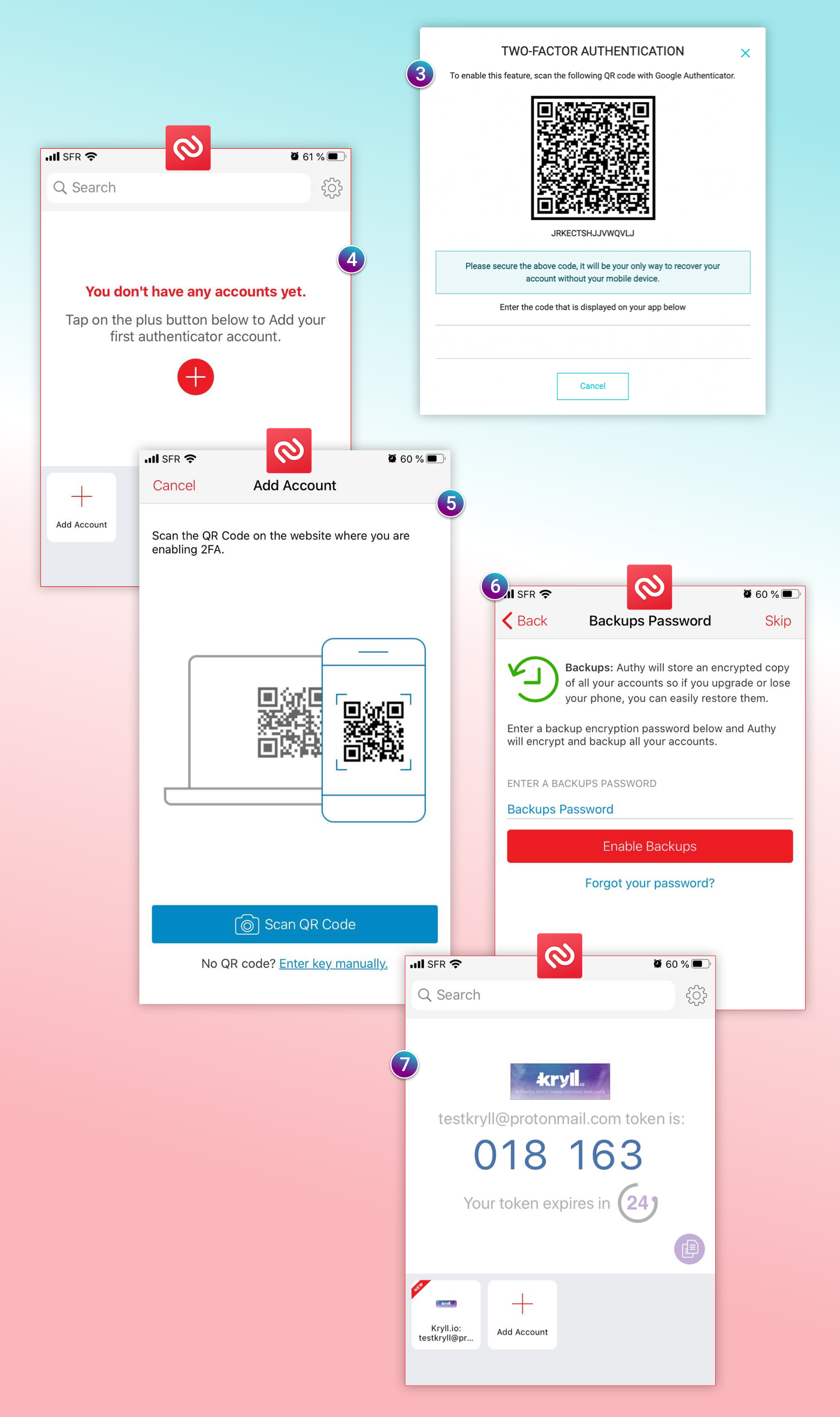
Step 3
The request for a new 2FA backup code was launched in the previous step and then a window opens with a new 2FA Kryll backup code that you can copy. Keep this window open for the final step of the process.
Step 4
Open the Authy application: "Add account."
Step 5
Paste the 2FA Kryll backup code in "enter key manually."
Step 6
The "backup password" option (on the Authy cloud) is highly recommended for those who have difficulties to secure their 2FA backup keys.
Step 7
To activate the 2FA Authy management service, copy the 2FA code then returns to the window of step 3 and complete the 2FA activation process which will finalize the 2FA Authy management with the link to your Kryll account.
Important reminder
Only the user owns the private 2FA backup key of his user account to connect to the dedicated 2FA management service.The exchange or a service like Kryll that offers 2FA does not know your 2FA backup key: it generates it only once in a secure computer program. The owner of the generated backup key is invited to secure it by himself or in the cloud via an external service like Authy backup.
"If you don't take the time to write down the private 2FA recovery key on a piece of paper (or encrypted digital files), it's best to use Authy and its secure backup on its cloud.
This can save you a lot of trouble especially when switching to a new phone without having access to the old one.
If you choose to stay on Google Auth and don't take care to secure your backup 2FA, you're exposing yourself to having your 2FA related user accounts inaccessible.
Going further
For your information, you also have a password management software like Bitwarden which is suitable if you have a lot of different passwords to manage or to share your password with your work teams without it being compromised.
Connecting with the physical key (not very mobile, but very secure) YubiKey or Ledger Nano and an anti-phishing code activated in the exchange settings are additional solutions to secure your Binance account, for example.
The "ideal" security with a good user experience is perhaps a combination of these different methods.
Website: https://kryll.io
Twitter : @Kryll.io
Telegram : https://t.me/kryll_io
Discord: https://discord.gg/PDcHd8K
Facebook : https://www.facebook.com/kryll.io
Support : support@kryll.io
